If you have ever considered the option of using encryption in your design, then you should be able to perform a side-channel attack as well as understand the consequences of such an attack on your product. While oscilloscopes and differential probes can be helpful in traditional power analysis attacks especially at the initial stage, these tools can be a bit of overkill for most analyses and also very expensive.
The ChipWhisperer series aims at nothing short of causing a fundamental change in the entire embedded security industry. A combination of documentation, training, open-source software and hardware makes it easy to master hardware security problems.
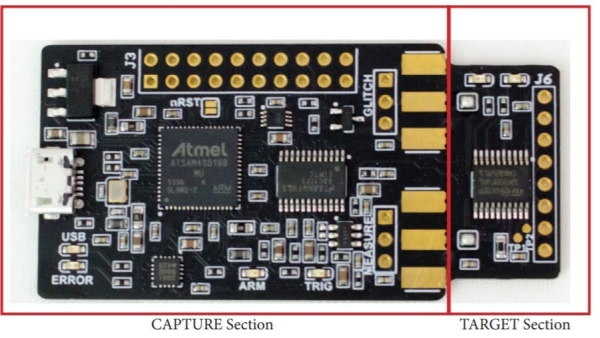
The new ChipWhisperer-Nano from NewAE technology is a small form factor tool that contains a capture device as well as an STM32- based target both for side-channel attacks and for learning. Designed primarily for power analysis demonstrations and training programs, this latest release in the ChipWhisperer series is an ultra-low-cost platform for voltage fault injection and side-channel analysis.
Some Of The Features Of The Chip Whisperer Nano Include:
- STM32F030 target for loading example code and a programmer built into the CWNANO.
- Crowbar based VCC glitching with about 10nS resolution on the width of the glitch and glitch offset from the trigger with up to 200nS jitter.
- ADC for sampling up to 20MS/s with either an internal clock (both synchronous and asynchronous) or an external clock (synchronous to the device).
- ADC hardware trigger that uses rising-edge input and samples for user-configurable length.
The ChipWhisperer NANO’s capture hardware has a dedicated 8-bit ADC chip interfaced with a microcontroller which helps to sample the power rail and provide information back to the software. It then provides frequency and timing analysis of the power signal while the target runs its algorithms.
Read more: PERFORM POWER ANALYSIS SIDE-CHANNEL ATTACKS WITH THE CHIPWHISPERER-NANO
