Jaydcarlson has posted on GitHub details about mxiot, which is a low-cost hardware prototyping platform, which enables you to explore switching small IoT projects from bare-metal to a secure-boot-capable WiFi/BT-connected Embedded Linux system capable of running rudimentary C/C++, and also applications written in almost any modern language or application framework (like Qt, Rust, Ruby, Python, Node.js, or .NET Core). At the core of mxiot is the i.MX6ULZ, a 900 MHz Cortex-A7 microprocessor. These are drop-in compatible with the i.MX6UL and i.MX6ULL.
The board features:
- 3 UARTs (one with hardware flow-control signals, and one dedicated to the console)
- Two I2C peripherals (one shared with one of the UARTs)
- SPI with 2 chip-select signals
- I2S with separate BCLK/WS signals for TX and RX paths.
- 4x PWM outputs
- Two USB ports
Apart from the DRAM and SD Card socket necessary for booting, mxiot also features WiFi and Bluetooth connectivity, 4x 12-bit analog inputs, care of the Texas Instruments TLA2024 APA102 addressable RGB LED QSPI Flash (that you can optionally boot from), and Pushbutton. WiFi and BLE are enabled via whatever 44-pin standard SDIO-interfaced WiFi/BT module du jour you’d like to add; the board supports all physically compatible Ampak modules.
The design is open-source, and more importantly, the BOM has wide availability and doesn’t lean on ICs with limited documentation or support. This means you can prototype your project around the mxiot and then copy the guts into your own design to optimize for size, power consumption, cost, or expanded functionality.
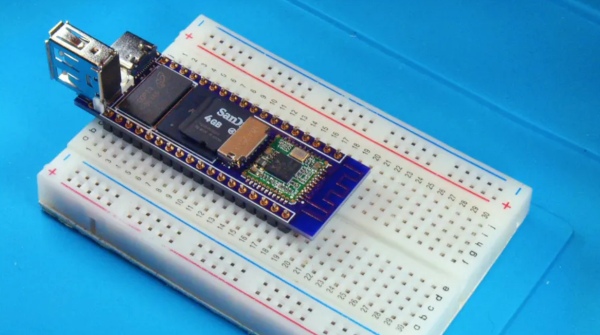
mxiot’s part are tightly arranged onto a dense 6-layer PCB measuring only 2.3 x 0.8 inches (58 x 20mm). The i.MX6’s OTP key storage, TrustZone, and secure-boot capabilities enable you to establish a chain of trust from the boot ROM to U-Boot, to the kernel, and an encrypted roots, which will enable you to store private data without you having to worry as much about physical device security. It also offers the ability to transport firmware updates over unencrypted channels, and you do not have to worry about your image being reverse-engineered or modified.
Read more: MXIOT, YOUR LOW-COST HARDWARE PROTOTYPING PLATFORM
